My Review of HackTheBox Prolabs #
Overview #
What are the Prolabs and why is this relevant? #
Prolabs from HackTheBox, are instances where there are many machines and networks present where you can ultimately test your exploit, pivoting and privilege escalation knowledge and capture flags in the process. There are many prolabs, and mini prolabs that you can tackle with each prolab having a different theme and simulating realistic corporate enviroments (well most of them). In this review i will go over the prolabs i have taken and shares my thoughts on them whilst giving tips/advice on what i wouldve done if i was retaking them. Also i will be sharing the prolabs in order i wish to take in the future!
Note, i have completed alot of the mini prolabs, i am only be going to reviewing the main, bigger labs.
First, lets talk about Dante! #

Context #
Just completing my eJPT around 3 months ago, i was still fresh off what i would call a “metasploit boy”, all i knew how to do was search for known exploits with searchsploit and type “getsystem” and hope for a system shell… jokes aside, i took Dante because my hacking experience as of then was only 1 host CaptureTheFlags. I probably had done around 20 easy and a couple medium machines from HackTheBox, when i heard that you could jump into whole networks! I should also note i had very little to no Active Directory experience and this was a huge learning curve for me at the time. I wanted to get started as soon as possible, though i was abit hesitant due to the pricey 50 ish dollars per month.
Review #
From a beginner standpoint and looking back at it now, Dante is an awesome first impression on hacking internal networks and a good way to get your hands dirty. Without giving too much away, in Dante you will be given an entry point IP, which essentially is the simulated publc facing web server (DMZ). You will have to enumerate and exploit this server, and use that server as a jumpbox (pivot) in order to reach the other internal network. From there, you are thrown into an Active directory enviroment, nothing too difficult but will definitely make you think if you haven’t tackled AD before. You will also need to priv esc a little bit. Overall i think Dante is a great lab for beginners, and i’d say for those of you who are planning to take eJPT, this is overkill but will prepare you no doubt for the exam.
Tips/Tools #
Here are some tips for begnners that are getting ready for Dante! -
- Learn BloodHound prior as tackling AD enviroments without this should be illegal (seriously)
- Create a cheatsheet for the impacket tools, and use them in a couple easy Active directory boxes before attempting boxes. (Impacket suite are incredibly useful)
- Learn either CrackMapExec or Netexec, and honestly research some of the modules. Alot of people dont know the full potential of Netexec, you can literally pwn most AD environments with this tool alone, no joke.
- Take good notes, you aren’t doing the labs to show off the certificate, remember the most important thing from all the prolabs is that you learn something new that you can use in the next challenge; its a constant loop of improvement.
- ligolo-ng, yep thats it..
- Dont be afraid to ask for help, the HackTheBox Discord community is really helpful, or message me personally (discord is .beejay)
Zephyr #

Context #
2 months after Dante, i decided to take Zephyr. I am following the famous OSCP box list spreadsheet, so i had done alot of the HackTheBox machines on the list, including every single Active Directory machine on the list. I had also done alot of the Vulnlab active directory chains and machines too. At this point also, i had taken a keen interest into Active Directory and red teaming. I started learning, to a basic understanding, learning a C2 (Command And Control Framework), as i had heard that this would massively aid me in these prolabs.
Review #
Zephyr consists of 17 machines and 17 flags over 3 domains. Zephyr was actually a really fun lab, with plenty of Active Directory exploitation involved where you can hone your skills and learn from. For me, the first domain was as smooth as can be, and the other domains took longer than they should have. I completed this pro lab in 3 and a half days, but i did this for around 10+ hours each of the days. The lab was stable some of the time but in my experience the lab was quite unstable at times, with alot of other players nuking ports and overall just overloading boxes with c2 implants. You may even find your attack path is easier than it should be due to other players changing the intended methods. Even after reaching enterprise admin, you still have to backtrack to reach hidden flags which i also didnt like, but overall i enjoyed Zephyr alot.
Tips/Tools #
- Learn, or start learning a C2 in the lab. There isn’t any obsurd evasion, but session management and efficient post exploitation will make you a better red teamer.
- Take organised and efficient notes. There are multiple domains, you will get lost very easily if you are not taking notes
- Everytime you find a new plaintext password or hash, add it to a wordlist and use it to spray against known usernames. You can use netexec to spray hashes and passwords accross subnets.
- Every time you compromise a machine, dump DPAPI secrets. You can use Lazagne or the netexec module to do this to make it more efficient.
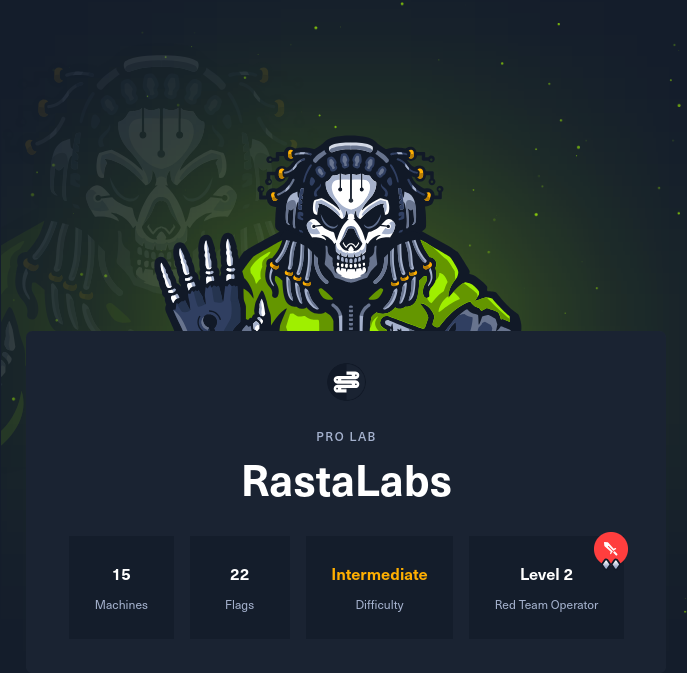
Rastalabs - TODO #